Eliminate Webex by Cisco Security Misconfigurations
Continuously monitor access controls & configurations
Start Your Free Trial
✓ Unify all native security controls into a single normalized view, to make your SaaS security incredibly simple to manage.
✓ Continuously monitor all your SaaS apps and detect any misconfigurations, incorrect permissions, and all possible exposure.
✓ Send detailed alerts at the first sign of a glitch or anomaly to stop minor incidents from becoming major problems.
Adaptive Shield integrates with Webex by Cisco in a click of a button. Once your trial is activated go to "Apps" and click on the Webex application to connect the app. Within minutes you will be able to oversee the security posture.
Connect with all your SaaS apps and easily control & optimize security across your entire stack


Connect with all your SaaS apps and easily control & optimize security across your entire stack


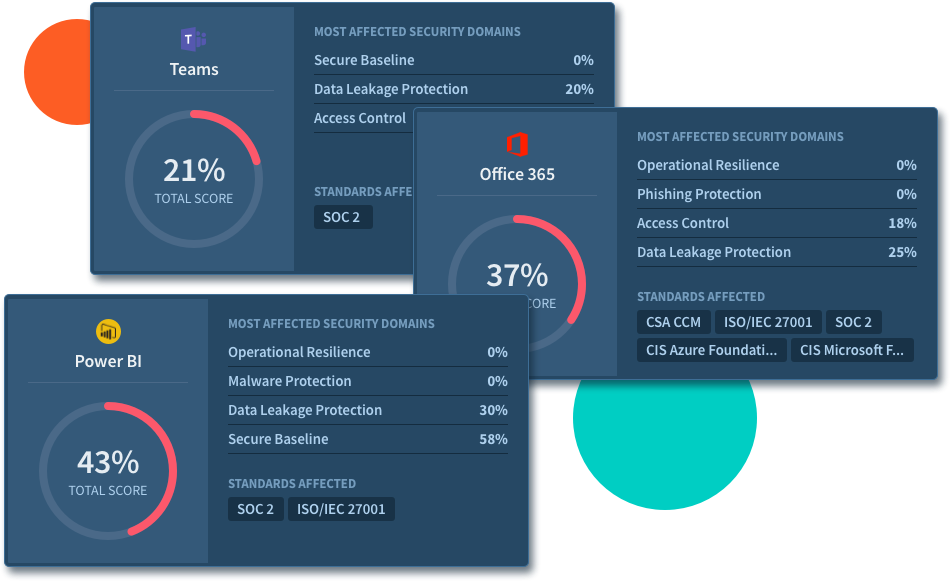
Enforce Cloud Security Controls & Prevent Misconfigurations and Exposure across SaaS Platforms
✓ Analyze all built-in security controls and settings✓ Identify exposure and misconfigurations
✓ Quantify security-related settings into a per SaaS and overall normalized posture score
✓ Benchmark against compliance frameworks
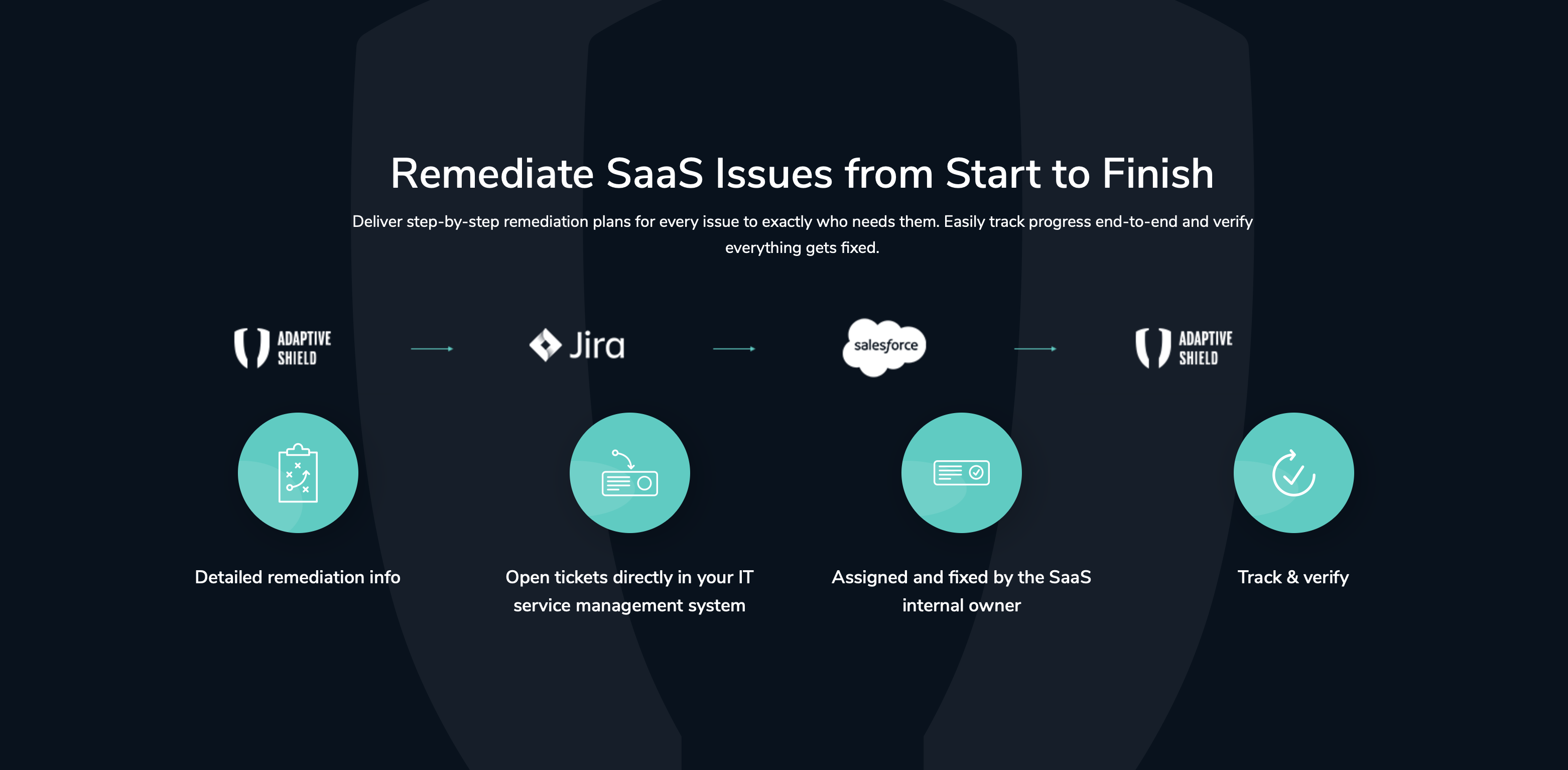
Remediation & Monitoring
✓ Automate remediation using ticketing with complete context✓ Track progress and alert on degradation and configuration drifts
✓ Follow trends over time
✓ Perform retrospective investigation
✓ Automatically maintain SaaS security best practices
User Cloud Access Governance
✓ Discover all your SaaS users, including employees, partners, and guests✓ Continuously measure each user level for possible exposure
✓ Identify users with excessive permissions
✓ Trim unused permissions and de-provision inactive users
✓ Identify and disable unsecured user authentication methods
Enterprise-Grade Platform
✓ ISO 27001 certified✓ Role-based access and granular user profiles
✓ Single sign-on support
✓ Automate alerts and notifications
✓ Audit users and system for vulnerabilities